Multilayer security is a vital strategy for protecting facilities and people. Investing in a comprehensive security system that incorporates multiple layers of protection is not simply an option, but an obligation for those who wish to safeguard their infrastructure and ensure their long-term resilience.
When a single incident has the power to cripple energy grids, transportation networks, or critical communications, the prediction and analysis of vulnerabilities becomes the most important defensive tool against emerging threats.
The First Step to Resilience: Vulnerability Analysis
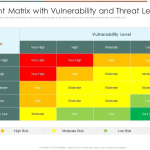
Vulnerability analysis is the foundational process in designing a resilient and secure environment for any critical infrastructure. This scientific approach allows us to move beyond intuition and rely on structured, evidence-based data to accurately estimate risk and design targeted protection measures.
A Two-Dimensional Approach to Security
Our methodology focuses on two core dimensions to provide a complete threat picture:
1. Threat Assessment
- Who is the potential attacker?
- What are their capabilities, motivations, and tactics?
2. Infrastructure Assessment
- Which elements are most critical?
- What value do they hold for the operator — and for the attacker?
The Ultimate Objective: From Vulnerability to Resilience
Through advanced algorithmic evaluation, we can transform raw data into actionable intelligence. The goal is clear: to move systematically from a state of vulnerability to one of proven resilience.
With rational planning, structured threat assessment, and a clear understanding of weaknesses, we can build infrastructures that endure — and more importantly, protect.
The ARGUS Strategic Solutions Approach
At ARGUS Strategic Solutions, as security consultants with extensive experience in physical security and critical infrastructure protection, we support organizations in implementing comprehensive vulnerability analysis methodologies. We believe modern security is built on a triad of prevention, knowledge, and strategic design.
Whether it concerns a private organization, an infrastructure operator, or a nation-state, the outcome of security is decided in the details.